
YOU
CAN'T
HACK
biometrics
When it comes to protecting your internet business, You don't want to be on
the ignorance is bliss only to Find Out The Hard Way Side
Grab The "Am I CyberSafe in the digital space?"
Phone App CyberSecurity Guide
And You Won't Have To...
When it comes to protecting your internet business, You don't want to be on
the ignorance is bliss only to Find Out The Hard Way Side
Register for The "Securista CyberSquad Workshops" Today
And You Won't Have To...
FROM THE CYBERSECURITY EXPERT WHO FOUND
THE 1ST SOCIAL MEDIA MALWARE
Layered

Home

Phone

Business
defense
As An Internet User, Protecting Everything, Especially Your devices, platforms, and personal information, is critical.
let's Protect your digital life
Your Data Is Your's
Text Message Opt-in
Here's a peek at What I Know
The Lockdown
Secure Your Business, Protect Your Future: Why Give Phishers The Phinger is a Must-Have for Women Entrepreneurs
Phishing Attacks aren't going away.
Securing our digital presence has become more crucial than ever, especially for women entrepreneurs who are navigating the fast-paced world of business.
Today, we're highlighting the importance of robust security measures for women entrepreneurs as we delve into the topic of securing Facebook against phishing scams. Let's talk about a solution that addresses social engineering threats and why ensuring a strong foundation for their online ventures is important.
With that said, Let's get started! 👊
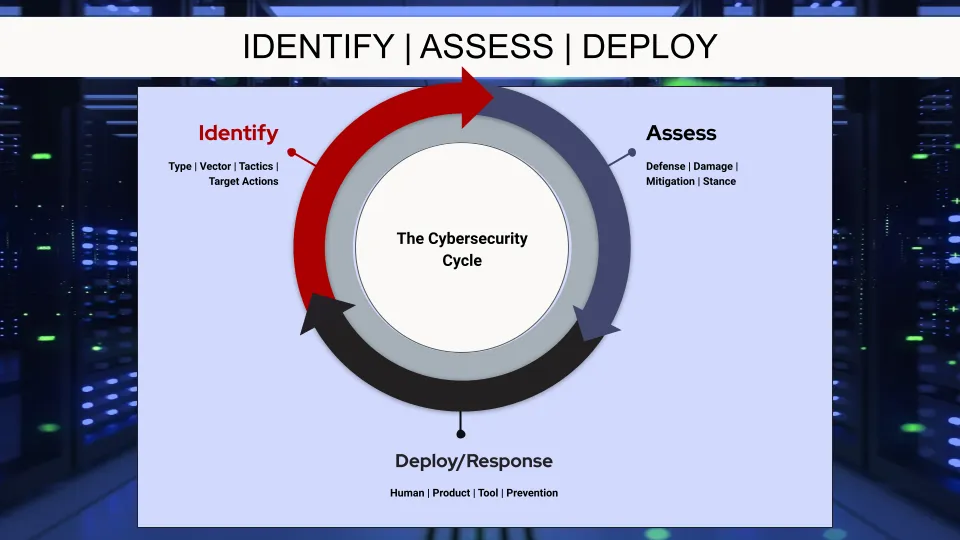
Understanding Social Engineering Threats
It's essential to understand the concept of social engineering so we can effectively protect ourselves from phishing scams.
Social engineering involves manipulating individuals into divulging sensitive information or performing actions that compromise their security. Phishing scams are a common form of social engineering, where attackers masquerade as trustworthy entities to trick their victims. We will explore various social engineering threat tactics, highlight common vectors used by phishers, and emphasize the importance of being able to identify these threats for effective prevention.
Assessing Current Security
Before implementing advanced security measures, it's crucial to assess the current security measures in place on our Facebook accounts. We'll provide guidance on evaluating these measures. Then we'll discuss potential vulnerabilities that can be exploited by phishers. Once we identify any weaknesses, we can take necessary steps to strengthen our security.
Deploying Advanced Security Tools
Facebook offers a range of advanced security tools and features that can significantly enhance our protection against phishing scams.
We will introduce these tools and explain how they can effectively prevent such attacks. Step-by-step instructions will be provided on enabling and utilizing these tools, empowering women entrepreneurs to take control of their online security. We will also highlight the benefits of using advanced security tools, ensuring peace of mind and uninterrupted business operations.
The Solution: Give Phishers The Phinger
Introducing Give Phishers The Phinger, a comprehensive workshop designed to secure Facebook against phishing scams.
This powerful resource helps women entrepreneurs identify social engineering threat types, tactics, vectors, and target actions.
With this knowledge, entrepreneurs can stay one step ahead of cybercriminals
The Reason:
In today's digital landscape, we start by securing your Facebook accounts against phishing scams and continue using the technique and tools to secure all your vital accounts.
We know the importance of robust security measures. Understanding social engineering threats, assessing current security, and deploying advanced tools often keeps your security measures cutting-edge.
By taking action and implementing strong security measures, we can protect our businesses and secure our future.
Remember, your business's security is in your hands. Give phishers the phinger and savor the secret pleasure it gives you.
Here's a peek at What I'm Up To
online DefendHer
01
GhostMode Cybersecurity workshops, Trainings, & Security Updates
I've got workshops and understanding cybersecurity trainings in the works. But if you need help you can book a security call. We'll cover protection and defense... securing your home networks and more. Then we'll tackle how to shield your privacy... out in the wild. Finally, learn the favorite techniques and products security experts use to shut down access to those all important social apps.
02
GhostMode Cybersecurity Trainings
I created the GhostMode Cybersecurity 101 & 201 Series to bring cutting edge, up-to-date security info and how to understand it. We'll cover AI, Web3, and even blockchain technologies in easy to understand every day language.
03
Consulting: security strategy & Security updates
We call the vulnerable point of attack an endpoint. We can start with a security audit and create a strategy of recommended products and services you can tailor to your home or business needs. You'll have access to recurring security updates and previews of what we're seeing in the cyberworld.
If I like you, I'll tell you about the Billion $ heist
Meet Your Security Expert
Oh Hello! I’m Angela "Ange Gos" Payton. I've reverse-engineered malware and as the tech copywriter, I made tech jargon understandable for everyday people. Retiring from the Security and Response team at Symantec didn't end my cybersecurity life.
My corporate copywriting clients, top competitors of my former company, wanted less technobabble in their marketing info, anchoring and keeping me deep in cybersecurity for years.
After several years of copywriting for competitors, why pivot to cybersecurity, now? I watched a "cybersecurity expert" with zero threat experience provide outdated information... so outdated, I knew I needed to help internet denizens, like yesterday because I have a wealth of knowledge and How-To's people need.
So here we are.
I live in a California Wine Country. It's a good Life!
Ready to Give A Phisher The Phinger?
Imagine keeping your family, home, AND business safe. Simply and easily.
What We Do...

what Others are saying...
“A really strong testimonial that confirms the transformation that is waiting.”
Lorem ipsum dolor sit amet, consectetur adipisicing elit. Autem dolore, alias, numquam enim ab voluptate id quam harum ducimus cupiditate similique quisquam et deserunt, recusandae. Lorem ipsum dolor sit amet, consectetur adipisicing elit. Autem dolore, alias, numquam.
Jane Awesome, ABC Co.
THE VALUE DOESN'T STOP THERE You'll Also Get These Benefits...
01
Guest speakers/trainers
Get To Know Some Seriously Smart People
I haz friends. I've already started inviting experts to come and talk about security trends and what's next. There may even be some history stories about how some threats were found.
02
The categorical list o'things
Apps, Tools, & SaaS Worth Considering
In the member's area, we'll have a dedicated set of lists for apps, tools, & SaaS (both Software as a Service and Security as a Service). We'll cover who's behind them and what they cover.

03
of course!
Security Isn't Sexy Until It Saves Your Ass
An ounce of prevention... yada, yada. But really, think of how cool it will feel to know the latest social phishing scams and shutting it down. That's where our courses come in. Based on the Categorical Lists O'Security, we break down the how so you can decide if it'll work great for your or keep your $$. We'll also offer courses that will the protection protocols you'll use often.

